The Ears of the World: Inside the ECHELON Surveillance Network
Introduction
For more than half a century, a clandestine web of listening posts, satellites, and hidden antennas has quietly intercepted global communications on a scale few could truly comprehend. Yet the uncomfortable truth is this: this vast surveillance empire is not operated by Moscow, Beijing, or Tehran – but by us. Born in the shadows of the Cold War, the system known as ECHELON has evolved from a single Anglo-American intelligence experiment into a sprawling global network, uniting the United Kingdom, the United States, and their closest allies in the intelligence-sharing pact known as the Five Eyes.
At its core, ECHELON is the mechanism that makes Five Eyes function; the invisible system through which the alliance listens, monitors, and understands the world. From the Yorkshire Moors to the deserts of Oman and Australia, remote Indian Ocean atolls, ECHELON’s reach is planetary. Its most remarkable feature, perhaps, is its unremarkable appearance: grey buildings and giant white radar domes that resemble golf balls scattered across far-flung and remote landscapes. Yet beneath these benign exteriors lie the most powerful eavesdropping systems ever built. Quite literally, ECHELON acts as the ears of the world.
This article examines ECHELON’s origins, evolution, and enduring strategic importance. It explains how a Cold War surveillance project became the backbone of the modern digital intelligence state, and considers what its continued existence reveals about Britain’s role within the Five Eyes alliance, and within the broader global order of intelligence and surveillance.
Origins: A Cold War Sword to Combat the USSR
The story of ECHELON begins in the aftermath of the Second World War, at a time when Western powers recognised that their resolute victory in future conflicts would depend not only on tanks, planes and ships, but on information. In 1946, the United Kingdom and the United States signed a secret pact known as the UKUSA Agreement. Its purpose was straightforward but revolutionary: to coordinate signals intelligence (SIGINT), the interception of radio, radar, and electronic communications, across the transatlantic pond.

RAF and USAF personnel on top of a newly constructed radome in 1962
Over time, the initial bilateral partnership was subsequently expanded to include Canada, Australia, and New Zealand, forming what became known as the Five Eyes alliance. Initially, their focus was strictly on monitoring the Soviet Union. Early ECHELON operations intercepted military radio traffic, microwave transmissions, and diplomatic cables across the USSR. Technology was simple, but effective. Massive antennas, tape recorders, and rows of intelligence analysts at Fort Meade in the US, and Cheltenham in the UK, working tirelessly to decode the vast amount of radio and communications chatter that ECHELON gathered from the Eastern Bloc and USSR.
ECHELON gave the West something close to omniscience. It provided real-time insight into Soviet submarine patrols, missile tests, and even domestic policymaking behind the Iron Curtain. As satellites began to revolutionise communications in the 1960s and 1970s, ECHELON’s reach expanded from terrestrial radio links, and moved towards orbital communications interception. What began as a handful of listening posts became a global network. ECHELON was invisible, automated, and became increasingly indispensable for the West.

Diego Garcia – The most secretive ECHELON Node
Expansion and Automation
By the late 1980s, ECHELON had outgrown its Cold War origins. With the Soviet threat fading, its capabilities were repurposed to serve broader intelligence needs. The modern threats faced by the West invoked a new era of counterterrorism, proliferation monitoring, and, some claimed, commercial espionage.
Reports from investigative journalists and the European Parliament revealed that ECHELON’s surveillance scope now extended to all forms of communication: telephone calls, faxes, emails, and, eventually, internet traffic. Instead of manually targeting individuals, the system used vast keyword databases, known as “dictionaries”, to automatically flag communications containing specific words or phrases such as “nuclear,” “embassy,” or “contract”, for example.
This newfound ability to automate ECHELON’s surveillance gathering marked a critical turning point. ECHELON became capable of filtering millions of global communications, of all domains, in real time. What had started as a Cold War tool for gathering military intelligence had evolved into a global-scale surveillance system, harvesting, analysing and storing billions of communications, every single day.
In the 1990s, allegations began surfacing that ECHELON was being used for economic espionage. French and German officials accused the United States and the United Kingdom of using intercepted intelligence from the ECHELON network, in order to benefit their own corporations in international trade negotiations. The Airbus–Boeing controversy, in which Boeing was accused of gaining access to classified information on European bids from the NSA, epitomised these concerns. Whether true or exaggerated, such claims blurred the line between national security and commercial espionage.
ECHELON’s Global Footprint
ECHELON’s true power lies not in any single installation, but in its vast, distributed architecture. ECHELON comprises a vast web of listening posts, satellites, and relay stations stretching across the globe. Each Five Eyes partner contributes regional coverage, ensuring that almost no corner of the electromagnetic spectrum escapes ECHELON’s interception.
The Main ECHELON Sites:
RAF Menwith Hill (UK) – Nestled in the Yorkshire Moors, Menwith Hill is the beating heart of ECHELON. Beneath its white radomes – the iconic “golf balls” – lies one of the largest intelligence-gathering complexes in the world. Officially a Royal Air Force station, it is effectively a joint NSA–GCHQ facility. It serves as the European hub for intercepting satellite and microwave traffic across Europe, Russia, and the Middle East.
GCHQ Bude (UK) – Situated on the Cornish coast in South Western England, the Bude facility intercepts transatlantic undersea fibre-optic cables that carry internet and phone traffic between North America and Europe. It encapsulates ECHELON’s modern evolution from satellite and radio interception, towards increasingly digital data capture methods. Bude is believed to have been central to TEMPORA, GCHQ’s mass data collection programme revealed by Edward Snowden in 2013.
Diego Garcia (British Indian Ocean Territory) – A remote atoll in the Indian Ocean and one of the most secretive military sites in the world. While officially a logistics hub, intelligence analysts believe Diego Garcia functions as a key ECHELON relay, monitoring communications across Africa, the Middle East, and South Asia. Its isolation makes it ideal for covert satellite interception and data transmission. For a more detailed look at Diego Garcia, please visit our article about the Chagos Islands.
Pine Gap (Australia) – Located deep in the Australian outback, Pine Gap is a joint US-Australian intelligence facility, forming the southern hemisphere’s primary satellite intelligence base. It tracks hostile missile launches, monitors radar emissions from adversaries, and intercepts signals across Asia and the Pacific. Pine Gap’s data flows directly into ECHELON’s shared analysis systems, subsequently being analysed by the NSA and GCHQ. Its geostrategic positioning makes Pine Gap one of the most strategically significant sites in the ECHELON network, being able to effectively monitor the increasing threat of China.
Waihopai Station (New Zealand) – Set, somewhat strangely, among Marlborough’s pristine vineyards, Waihopai historically intercepted satellite communications across the South Pacific. Though the site has been partially mothballed in recent years, it remains operationally vital to the ECHELON network, representing New Zealand’s contribution to the Five Eyes’ collective coverage.
CFS Leitrim (Canada) – Canada’s principal signals intelligence facility, located in Ontario, monitors North Atlantic and Arctic transmissions. It integrates northern coverage into ECHELON’s architecture, ensuring that even polar communications are intercepted and analysed.
RAF Seeb (Oman) – Operating near the Strait of Hormuz, Seeb monitors Middle Eastern and Indian Ocean communications, including fibre-optic routes linking Asia and Africa. It plays a crucial role in tracking maritime traffic and regional threats, and was recently utilised extensively for intelligence gathering and counter-terror operations during Anglo-American operations against Yemeni Houthis in 2024.
Together, these sites form the operational skeleton of ECHELON, each specialising in different regions and data types, yet feeding into a single, seamless, automated analysis network. In real-world practice, the USA’s NSA provides most of the computing infrastructure and data storage, while GCHQ supplies regional access and analytical expertise, especially across Europe, Africa, and the Middle East.
Though its technologies have evolved from antennas to fibre optic taps, reflecting the way in which global communications have advanced, ECHELON’s essence remains unchanged: a distributed surveillance system quietly collecting, filtering, and archiving the world’s communications. Hidden beneath its anonymous radomes, it continues to serve as the invisible nervous system of the Five Eyes alliance. It serves as a reminder that, even in the digital age, the art of listening still defines global power.
Above: An interactive map showing Global ECHELON Nodes
Exposure and Public Awareness
For decades, ECHELON was an open secret: referred to by whistleblowers and journalists, but never acknowledged in full by participating governments. The first major public account came from investigative reporting and parliamentary inquiry at the turn of the millennium. In 2000–2001, the European Parliament’s temporary committee, prompted by reporting from journalists such as Duncan Campbell, produced an extensive investigative report, confirming the existence of a global interception capability operated by the UK and US governments. The committee warned that it “may be capable of intercepting private and commercial communications on a global scale.” The report fuelled controversy in Europe about transparency, industrial espionage, and legal oversight.
The public debate flared again in 2013 after documents were famously leaked by US Government whistleblower Edward Snowden. Snowden’s disclosures showed that the principles underpinning ECHELON: mass interception, automated filtering and keyword selection, and broad international sharing, had been extended and modernised into separate programs such as the NSA’s PRISM and GCHQ’s TEMPORA programs. Reports from the Guardian, based on Snowden’s files, revealed that GCHQ had been tapping fibre-optic cables, as well as using large data stores to process vast volumes of internet traffic in near-real time. The post-Snowden revelations forced a global reckoning over how democratic states collect, store and use their citizens’ communications data, and sparked debate over how ethical, and necessary, these practices are.
Despite these exposures, key elements of ECHELON’s capabilities remain classified. What changed most was not the existence of the network, but public awareness of its scale and technological sophistication. Once a Cold War conspiracy theory, whispered about in intelligence circles, ECHELON became the blueprint and the case study for 21st century mass surveillance. Ultimately, the Snowden files prompted the shifting debate from “does it exist?” to “how should it be governed?”.
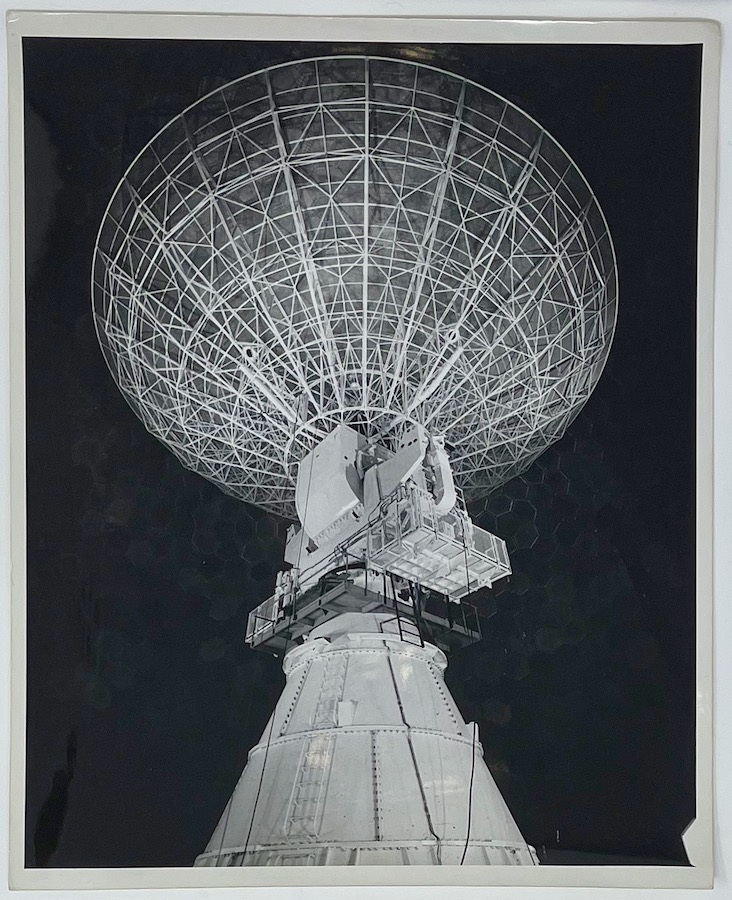
A view of an ECHELON Satellite Ground Station
Britain’s Role and the Legal Framework
The United Kingdom has been central to both the intelligence-gathering architecture, as well as the global reach of ECHELON. GCHQ, Cheltenham’s iconic “doughnut”, is the UK’s primary signals-intelligence hub, and a chief Five Eyes partner. Historically, Britain’s value to the alliance has been geographic, providing global facilities for satellite visibility (such as Diego Garcia), cable landing stations (such as Bude) and a longstanding SIGINT expertise. In return for this, the UK gains privileged access to US infrastructure, intelligence processing power and data. This is a trade that has been instrumental in underpining London’s post-imperial global relevance, and is a major contributor to the transatlantic defence partnership.
The UK’s intelligence-gathering powers operate within a complex legal framework domestically. The Intelligence Services Act of 1994 formally established GCHQ in law, and subsequently introduced mechanisms for more parliamentary oversight over its activities. More recently, the Investigatory Powers Act of 2016, often called the “Snoopers’ Charter”, spelt out the UK’s interception, data retention, and hacking powers. It added judicial approval for warrants through a “double-lock” system and created new surveillance oversight bodies, able to better hold GCHQ to account for domestic data gathering. Supporters argue the 2016 Act brought greater transparency and legal certainty. Critics, however, claim it effectively legitimised GCHQ’s mass surveillance network, ECHELON, and left unresolved questions about proportionality, privacy, and accountability. In essence, Britain sits at the heart of the global intelligence network with a legal system designed to regulate it, but one that still struggles to keep pace with the rapid evolution of surveillance technology. Possibly, however, for the uninterrupted effectiveness of GCHQ, a lack of a proactive legal approach towards surveillance, is, operationally, a positive.

GCHQ’s Cheltenham Facility “The Donught”
From Satellites to Servers: ECHELON in the Digital Age
ECHELON’s original signal interception methods were archived via satellite and radio interception. It has, however, been forced to adapt to the modern age. Its modern iteration operates primarily by intercepting internet traffic. The technical transition from microwaves and satellites to fibre-optic internet traffic is the defining change of the past 30 years. Rather than listening for spoken words on HF radio, modern systems capture metadata, data packets and IP addresses from undersea fibre cables, cloud providers and social media platforms. This is something that can be reflected in Open Source Intelligence, something I personally experienced at the University of York’s Intelligence and Defence Society. Analysing data on the internet is surprisingly simple, even with basic tools, and for GCHQ it presents an opportunity to rely less on geographically positioned radio and satellite intercept stations. After the Snowden files release, NSA and GCHQ programs such as “PRISM” and “TEMPORA”, showcase exactly how, principally, the same “collect-everything, filter-later” Cold-War era surveillance logic has been ported into the internet age, and has been ramped up, at scale, to cater to the world’s transition to a digitally focused existence.
Two main technological shifts have been instrumental in transforming ECHELON’s modern-day surveillance capabilities. First, scale: today’s fibre-optic cables and global cloud infrastructure, run by companies such as Google, now carry vastly more data than the Cold War’s satellite links were capable of. Advanced data storage systems, such as the “bulk buffers” reported at GCHQ Bude, enable intelligence analysts to store and retrospectively search through enormous datasets spanning months or even years. Second, automation: machine learning and advanced pattern-recognition tools have replaced the manual keyword searches of the Cold War era. Where analysts once relied on keyword lists, today’s systems use complex algorithms and “selectors” to determine suspicious internet activity. With an increase in global capacity and data, there has also come more “noise”. This is why advanced algorithms to automatically filter and determine what transmissions and communications should be flagged are so instrumental. Technical reports of ECHELON describe advanced “Torus” antennas and multi-petabyte internet traffic data collection systems feeding this filtration process, which, when combined together, provides the Five Eyes alliance with a near-real-time map of the world’s communications traffic.
Operationally speaking, this modern shift delivers both increased surveillance capability and controversy: it improves ECHELON’s speed and global coverage for legitimate security tasks, such as counterterrorism and cyber defence, but it also increases the chance of incidental collection of private or sensitive data.
Criticism and Controversy
The ECHELON surveillance network has attracted a number of widespread criticisms:
Privacy and civil liberties: Bulk interception techniques, such as those employed across the Five Eyes Network, capture huge volumes of ordinary citizens’ communications. Some courts have argued that mass collection, even when filtered, infringes on privacy norms and human-rights protections unless tightly constrained and transparently overseen. This type of oversight is something which is not currently present, at least in the UK and USA. Legal reviews and tribunal findings in the UK and Europe have repeatedly pressed intelligence services to justify bulk data retention of citizens and to increase transparency of their surveillance operations.
Industrial espionage: The European Parliament’s inquiry and journalists’ reports raised the possibility that SIGINT could be used for economic leverage. High-profile allegations, such as the Boeing-Airbus case, never produced ironclad public proof; however, these allegations crystallised fears that intelligence networks, such as ECHELON, could be repurposed for national commercial advantage.
Democratic accountability: The sheer technical complexity of modern surveillance and intelligence gathering makes democratic oversight, and public scrutiny, inherently difficult. While parliamentary committees, independent reviewers, and tribunals do exist to provide scrutiny, the secrecy required to protect intelligence sources and the effectiveness of surveillance methods limit what can be examined publicly. In order to protect the effectiveness of surveillance networks such as ECHELON, organisations such as GCHQ are afforded a huge amount of protection from the public eye. The balance remains problematic: effective intelligence depends on secrecy, yet democratic legitimacy demands transparency and accountability.
International law and norms: Because ECHELON’s operations are global in scale, they raise difficult questions about sovereignty and legal jurisdiction. If a UK-based interception point captures data routed through foreign networks, which country’s laws apply, and does the UK have any right to this data?
In essence, what the ECHELON network has pioneered: mass, automated, and cooperative surveillance, provides undeniable strategic advantages; however, it continues to pose profound ethical, legal, and political questions.
What ECHELON Means for UK Foreign Policy
ECHELON matters greatly for Britain, not only because of the intelligence it collects, but because of what it permits politically.
Soft power and influence: Membership in the Five Eyes alliance grants the UK significant diplomatic influence in security forums. Intelligence sharing, threat assessments, and operational cooperation bolster the UK’s standing in NATO, the UN, and with partners lacking similar capabilities, giving the UK leverage in global diplomacy. Essentially, intelligence acts as a form of influence currency.
Strategic reliance and alignment: This influence comes with a cost: the UK is a partner within an asymmetrical system, primarily led by US resources and guidance. The UK’s dependence on NSA infrastructure and US satellite assets can constrain UK policy choices and align British intelligence closely with Washington’s strategic goals.
Reputational considerations: Pursuing normalisation or legalisation of mass surveillance carries reputational risks, especially in the “Global South” and among liberal allies. The Chagos sovereignty debate is a useful analogy, highlighting how diplomatic capital is finite. Actions perceived as unfair or extrajudicial risk damaging the UK’s moral standing on the international stage. Similarly, unchecked surveillance can weaken Britain’s soft power, even if it enhances operational capabilities and domestic security.
Security benefits: Finally, practical security gains include disrupting terrorist plots, supporting coalition efforts, and providing early alerts of hostile cyber or military threats. These tangible results are a primary reason intelligence agencies defend the current framework.
Combined, ECHELON’s legacy is a double-edged sword for British foreign policy: it amplifies influence but also obliges the UK to an intelligence system whose priorities and potential reputational costs require careful management.
Conclusion
ECHELON began as a Cold War instrument to pierce the Iron Curtain. Over decades, it has been modernised, broadened, and woven into a global fabric that now intercepts the digital heartbeat of the planet. For Britain, the network has delivered strategic relevance, privileged intelligence access, and practical security benefits. But it has also introduced profound legal, ethical and political dilemmas about privacy, democratic oversight, and dependence on powerful allies.
The question for Britain is not whether to possess such capabilities. In an increasingly hostile world, surveillance capability is unavoidable, but instead the debate has shifted towards how to govern such capabilities. Finding the right balance between public transparency, and ensuring the continued effectiveness of surveillance networks is an increasingly difficult tightrope for intelligence powers to tread. ECHELON’s story is not only an account of extraordinary technical reach; it is a lesson in the limits of secrecy and the duties of democratic accountability.
